William Weber, a LowEndTalk member, was raided by Austrian police in 2012 for operating a Tor exit node that was allegedly used to distribute child pornography. While he was not arrested, many of his computers and devices were confiscated. He was later found guilty of supporting the distribution of child pornography through his Tor exit node, though he claims it was unintentional and he was simply supporting free speech and anonymity. He was given a 5 year probation sentence but left Austria shortly after. Though some articles portray him negatively, it is debatable whether he intentionally supported child pornography distribution or simply operated in the legal grey area of Tor exit nodes.
We oughtta arrest the people who pave roads because human traffickers use them to commit crimes.
I wonder if the ISP got charged as well lol
The charges usually end up falling onto the last one who can’t stick them onto someone else.
Like, a carrier can blame the ISP, who can blame the VPN, who can check its logs and blame an address owner, who… better keep their own logs capable of identifying someone else if they’re letting random people do random stuff using that address. And a good lawyer, and will and money to fight it.
From the article…
Yes, as they had to give me the minimum sentence. By law they were right as the law only protected registered companies, unlike in Germany for example. The law was changed a few weeks later to include private persons and sole traders as protected lsps, not just companies, but they had to convict me. No choice in the end.
So, ISPs in Austria actually have legal protection from liability here, rightfully so, and also rightfully so, that protection was extended to private persons as well. A rare story of a legal system apparently working well, with regard to the marriage of privacy and technology.
Do they not have Jury Nullification over there?
Shouldn’t all social media, ISPs, Apple, Google, etc also be found guilty of the same crime then? What about CDN?
The article explains that this was basically a flaw in the way the law was written
Reading the article, it’s not just distributed CP. Someone also used his Tor Exit to hack into a NATO facility in Poland that dealt in chemical/biological weapons. Like, yeeesh.
This “someone” sounds an awful lot like a nation-state actor.
Yikes 😬
I’m surprised this doesn’t happen more often. Home routers are trivial to compromise, and compromised home routers can also be used to distribute illegal content.
This is equivalent to a criminal running into a crowd to get away from police, and the police just stopping, arresting, and charging the first person in the crowd that they see for not doing anything to stop them.
Btw, what’s the current judicial status of exit nodes around the world? Why was he charged, yet the isp wasn’t? Would the isp be charged if it ran a similar exit node, or is it strictly because it was a private entity?
Rule of thumb: You get the blame.
TL;DR: Ask a lawyer.
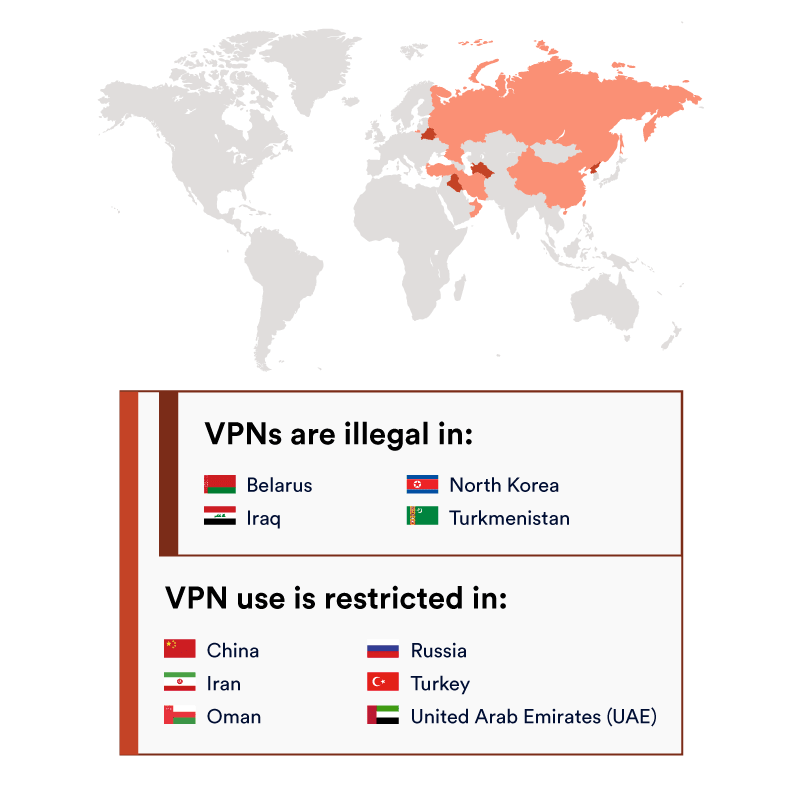
You can compare them to VPNs for the severity of restrictions (in 2020):
For some more historical info, there is this list on Wikipedia: https://en.m.wikipedia.org/wiki/Tor_(network)#Reception,_impact,_and_legislation
For a more US-centric FAQ, you can check: https://community.torproject.org/relay/community-resources/eff-tor-legal-faq/
Still, most countries don’t like random people to let other unidentified random people to do random stuff, most police officers are ill equipped or educated to deal with it, legislation hasn’t been tested in most places, and you’re running a hard to define, changing, and sometimes random level of risk.
we should have separate dark web(no CP) and dark web(CP)
Yes we should. How would you go about doing that?
Put it in the dark web’s terms of service.
Imagine trying to enforce such a thing on the dark web. What would you call the people who would end up with that job?
Start two dark webs, fill one with CP… and all the CP users will go to that one? Or something /s
Put a CP detector at dark web(no CP) exit nodes and throttle the speed to shit when triggered?
Oh yeah, packet sniffing exit nodes in a privacy oriented network will surely go down well and will have no unforeseen consequences
It’s been working fine for 20+ years already, with consequences foreseen from the beginning:
- Don’t trust exit nodes, they get the final packets and can do with them whatever they want.
- If you put identifying data in an unencrypted packet, the exit node will know who you are.
- If you send identifying data (encrypted or not) to a website, the website will know who you are.
- Trust destination websites only barely more than you’d trust them normally, and only as long as you keep the NoScript enabled.
- If your entry node colludes with your exit node, they might analyze data traffic patterns to try and identify you.
If you want to hide your porn habits from your techie flatmate with a logging router, Tor works great. If you’re a CIA agent in Iran wanting to send some report back home without getting found out, Tor works great. If you’re a whistleblower wanting to send an anonymous tip to the Washington Post, Tor also works great. If you’re curious to see that foreign mercenary group’s website that’s blocked in your country… SWIM had to try some different circuits, but Tor also worked there.
What do you mean? The exit nodes runners are doing the heavy lifting here. It’s fair for them to do everything technically possible to avoid unwanted raids.
Lol
I mean it’s an exit node and the open web you don’t really get to complain about lack of privacy when leaving Tor.
OTOH, there’s a simple problem: That traffic is still likely encrypted. It’s not like Tor exit nodes do the TLS handshake, do they? That would indeed be much stranger than applying traffic shaping.
Sure, but preinstalling packet snooping on exit nodes as a feature still doesn’t sound like a great move, nevermind how stupid the idea is exactly because, like you said, HTTPS is a thing
How would that possibly work?
The absolute balls on the man to continue after being raided. It’s unfortunate that the private internet requires people like him to risk their safety so it can continue to operate.